3CX Becomes First Known Victim of a Cascading Supply Chain Cyberattack
Saturday, 22 April 2023
VoIP communications company 3CX provides a phone system that is used by over 600,000 companies worldwide, and attracts over 12 million users daily. Some of its customers include high-profile companies and organisations such as Air France, American Express, Coca-Cola, IKEA, and McDonald's.
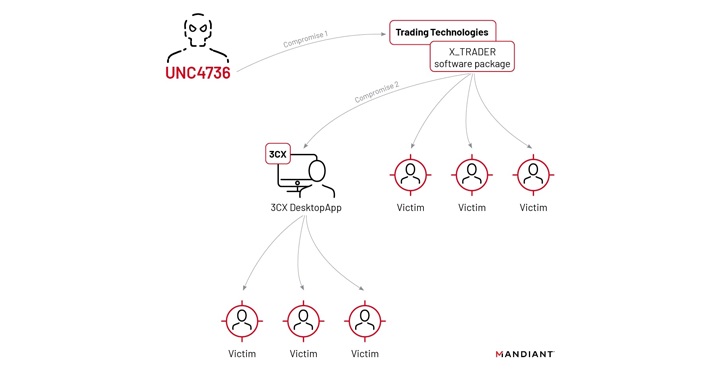
Although not the original target of the attack, 3CX will go down in history as the first ever known victim of a 'cascading supply chain' cyberattack. Mandiant, a subsidiary of Google, is tracking the attack under the moniker UNC4736, and said the incident marks the first time it has seen a "software supply chain attack lead to another software supply chain attack."
Concerns are being raised regarding the ties between UNC4736 and North Korea, with 3CX CISO Pierre Jourdan stating today that "Based on the Mandiant investigation into the 3CX intrusion and supply chain attack thus far, they attribute the activity to a cluster named UNC4736. Mandiant assesses with high confidence that UNC4736 has a North Korean nexus."
Mandiant's investigation into the sequence of events has now revealed that the attack began with a compromised piece of software called X_TRADER, which was owned by a company called Trading Technologies. This compromised software was downloaded by a 3CX employee onto their personal computer on March 29th. The day after, 3CX revealed that its 3CXDesktopApp desktop client was compromised and used to deploy malware known as Taxhaul (or TxRLoader).
Taxhaul in turn deployed a further malware downloader dubbed Coldcat. This final piece of malware came with in-built persistence mechanisms making it harder to remove, automatically loading into memory on system startup. Additionally, it disguised itself by making use of legitimate Microsoft Windows binaries, which meant that it was harder for antiviral products to detect.
Malware deployed onto Windows computers connected to multiple command-and-control (C2) servers owned by the hackers, which masqueraded as legitimate IT providers such as Akami and Azure, while Apple systems targeted by the attack had a different piece of malware dropped onto them - Simplesea. The team at Mandiant is currently still assessing whether or not Simplesea overlaps with previously known malware families.
"Supported backdoor commands include shell command execution, file transfer, file execution, file management, and configuration updating. It can also be tasked to test the connectivity of a provided IP and port number," Jourdan added. Security vendors CrowdStrike, ESET, Palo Alto Networks, SentinelOne, and SonicWall began flagging the 3CXDesktopApp product as malicious, while 3CX advised customers to uninstall the client.





