Flaw in WiFi Protocol Allows Hijacking of Network Traffic
Saturday, 8 April 2023
A flaw in the design of the IEEE 802.11 WiFi protocol standard itself could allow hackers to trick WiFi access points into leaking encrypted network data as plaintext. This would mean that all data sent across a WiFi network would be easily readable by hackers.
WiFi data is normally encrypted as a combination of header, data payload, and trailer frames. They include information pertaining to both the source and destination, along with information on how the recipient should control and manage the data. These frames are transmitted in an algorithmically controlled manner, allowing the avoidance of collisions, and maximising performance.
However, researchers Domien Schepers and Aanjhan Ranganathan of Northeastern University, along with Mathy Vanhoef of Katholieke Universiteit Leuven, found that queued frames are not adequately protected, allowing manipulation of data transmission, client spoofing, frame redirection, and capturing. "Our attacks have a widespread impact as they affect various devices and operating systems (Linux, FreeBSD, iOS, and Android) and because they can be used to hijack TCP connections or intercept client and web traffic."
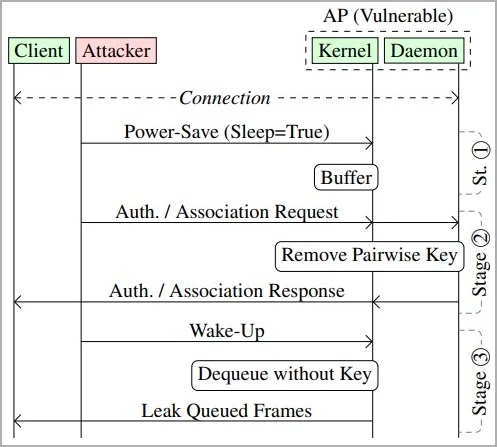
IEEE 802.11 is designed to queue frames destined for sleeping devices, so that they can resume transfer when the device awakens. However, the standard does not provide explicit guidance on how the security of these queued frames should be managed, and does not set limitations on how long the frames can stay in a queued state. Attackers can change the security context, forcing frames to be transmitted in plaintext.
Device models from Lancom, Aruba, Cisco, Asus, and D-Link are reported to be affected by these attacks.
The researchers warn that such attacks could be used to inject malicious JavaScript directly into TCP packets. "An adversary can use their own Internet-connected server to inject data into this TCP connection by injecting off-path TCP packets with a spoofed sender IP address," warn the researchers. This can, for instance, be abused to send malicious JavaScript code to the victim in plaintext HTTP connections with the goal of exploiting vulnerabilities in the client's browser."
Cisco is the first vendor to acknowledge the vulnerability, admitting that the attacks outlined in the paper may be successful against Cisco Wireless Access Point products and Cisco Meraki products with wireless capabilities. Mitigation measures like using policy enforcement mechanisms through a system like Cisco Identity Services Engine (ISE) are recommended by Cisco. "Cisco also recommends implementing transport layer security to encrypt data in transit whenever possible because it would render the acquired data unusable by the attacker," reads the Cisco security advisory.





